sentinelchangelog.net: Auto-Generated Summaries of Every Sentinel Content PR
The Azure/Azure-Sentinel repository gets merged PRs constantly. New detections, connector fixes, KQL function updates, hunting query changes. There’s no official changelog. If you want to know what changed, you either watch the repo and get buried in notifications, or you don’t, and you miss things that matter.
I built sentinelchangelog.net to address that.
What it covers
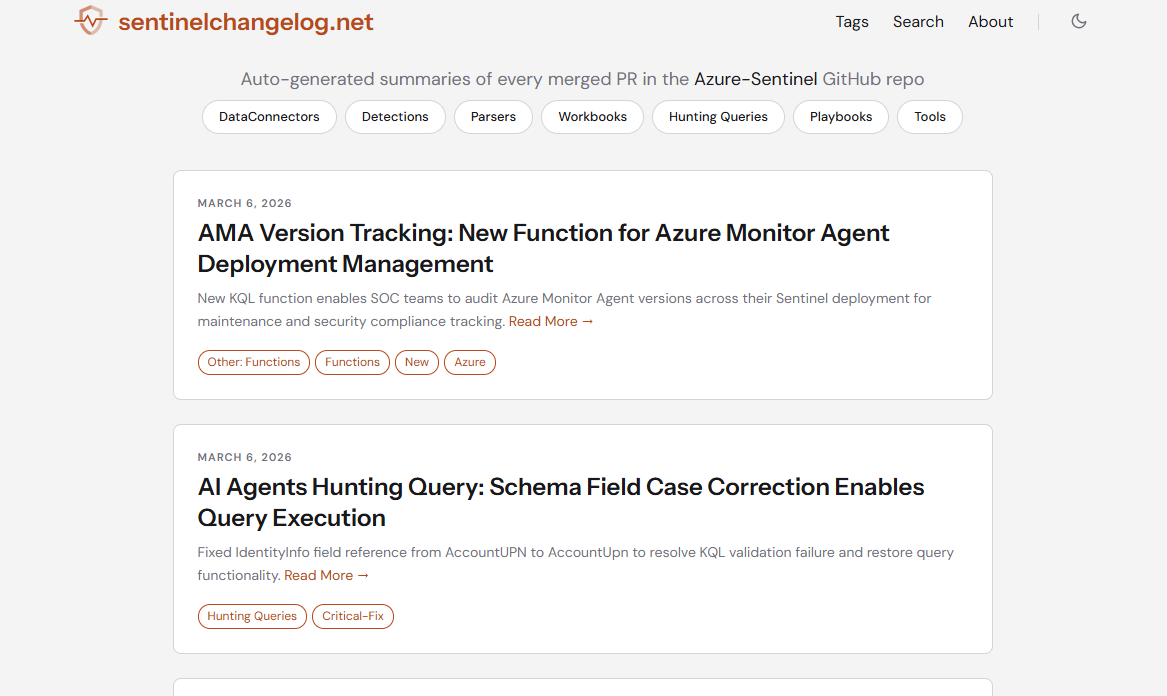
The site monitors the Azure/Azure-Sentinel repository for merged pull requests and publishes a structured post for each change that has operational relevance. Changes that are cosmetic, version-bump-only, or otherwise carry no signal for defenders are skipped.
Content is organised by type: detections, data connectors, hunting queries, workbooks, playbooks, parsers, and tools. The main page has category filters and a full-text search, so you can narrow to just the content types that matter for your environment.
What each post looks like
Each entry is structured around what a detection engineer actually needs to know:
- Summary - one sentence on what changed
- Security Impact - what visibility was gained, lost, or restored; whether detection gaps opened or closed
- Affected Files - which rules, connectors, schemas, or queries changed
- Rating - Critical, High, Medium, Low, or Informational
- Action - what you should do: Immediate Fix, Review, Update, Monitor, or No Action
- View on GitHub - direct link to the source PR
The honest bit
Posts are AI-generated. The model analyses the code diff and available PR metadata to assess security relevance, generate the summary, and assign the rating and action classification. It does a reasonable job on well-described PRs. It struggles on the ones where the author committed five files with a message like “update” and no description, which is not uncommon in the upstream repo - especially with some of the big 3rd party vendors.
The model can also misread intent, miss context that exists only in a verbal discussion outside the PR, or get severity wrong in edge cases. A Critical rating means the model assessed it that way based on the diff. It doesn’t necessarily mean you need to drop everything. When something looks important, the View on GitHub link is there to check the source.
Treat each post as a triage signal, not a definitive assessment. That’s how I use it.
Who it’s actually useful for
Detection engineers, SOC analysts, and implementation consultants like me who want to know when something relevant changes in the built-in Sentinel content library without having to monitor GitHub themselves. It’s particularly useful if you’ve deployed community detection rules, or if you’re running connectors sourced from the repository. Rather than periodically checking whether the version you deployed is still current, the site surfaces relevant changes as they’re merged.
It’s also handy as a historical reference. When someone asks “was there a recent change to this detection rule?” the full change history is searchable rather than requiring a trawl through GitHub.
The site is at sentinelchangelog.net. It’s just an unofficial side project of mine, and not affiliated with or endorsed by Microsoft.